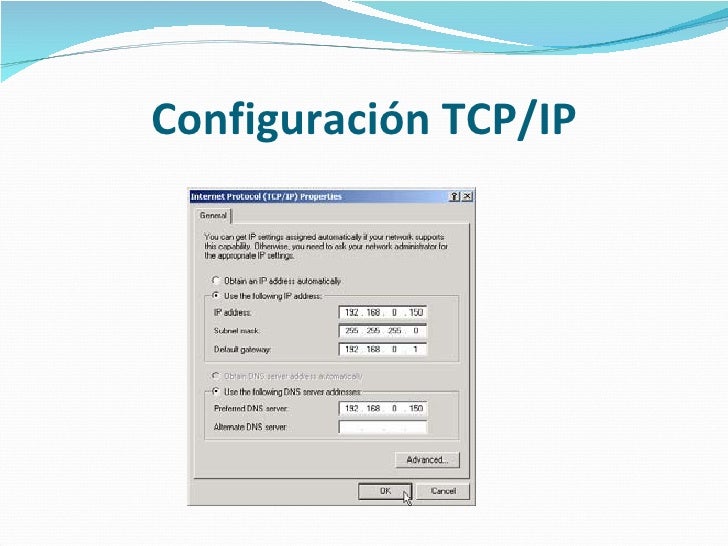
By default, MAC OS X is configured as a DHCP client. However, if MAC OS X has been configured with a static (manually configured) IP address, and if the computer needs to receive an IP address automatically, then MAC OS X will need to be reconfigured as a DHCP client. Manually configure IPv4 TCP/IP parameters from the control panel. Open the following menus: Network Setup. TCP/IP configuration. Use the arrow.
The two protocol components of TCP/IP deal with different aspects of computer networking. Internet Protocol, the 'IP' of TCP/IP is a connectionless protocol which deals only with network packet routing using the IP Datagram as the basic unit of networking information. The IP Datagram consists of a header followed by a message. The Transmission Control Protocol is the 'TCP' of TCP/IP and enables network hosts to establish connections which may be used to exchange data streams. TCP also guarantees that the data between connections is delivered and that it arrives at one network host in the same order as sent from another network host.
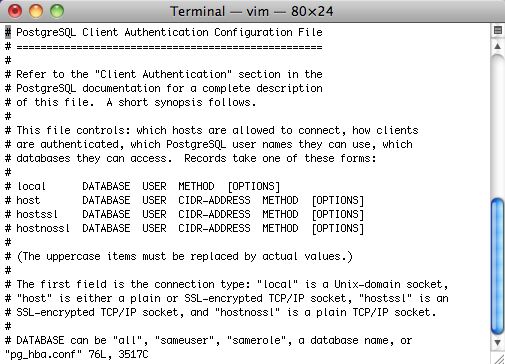
The TCP/IP protocol configuration consists of several elements which must be set by editing the appropriate configuration files, or deploying solutions such as the Dynamic Host Configuration Protocol (DHCP) server which in turn, can be configured to provide the proper TCP/IP configuration settings to network clients automatically. These configuration values must be set correctly in order to facilitate the proper network operation of your Ubuntu system. The common configuration elements of TCP/IP and their purposes are as follows. IP address The IP address is a unique identifying string expressed as four decimal numbers ranging from zero (0) to two-hundred and fifty-five (255), separated by periods, with each of the four numbers representing eight (8) bits of the address for a total length of thirty-two (32) bits for the whole address. This format is called dotted quad notation. Netmask The Subnet Mask (or simply, netmask) is a local bit mask, or set of flags which separate the portions of an IP address significant to the network from the bits significant to the subnetwork. For example, in a Class C network, the standard netmask is 255.255.255.0 which masks the first three bytes of the IP address and allows the last byte of the IP address to remain available for specifying hosts on the subnetwork.
Network Address The Network Address represents the bytes comprising the network portion of an IP address. For example, the host 12.128.1.2 in a Class A network would use 12.0.0.0 as the network address, where twelve (12) represents the first byte of the IP address, (the network part) and zeroes (0) in all of the remaining three bytes to represent the potential host values. A network host using the private IP address 192.168.1.100 would in turn use a Network Address of 192.168.1.0, which specifies the first three bytes of the Class C 192.168.1 network and a zero (0) for all the possible hosts on the network. Broadcast Address The Broadcast Address is an IP address which allows network data to be sent simultaneously to all hosts on a given subnetwork rather than specifying a particular host. The standard general broadcast address for IP networks is 255.255.255.255, but this broadcast address cannot be used to send a broadcast message to every host on the Internet because routers block it. A more appropriate broadcast address is set to match a specific subnetwork. For example, on the private Class C IP network, 192.168.1.0, the broadcast address is 192.168.1.255.
Broadcast messages are typically produced by network protocols such as the Address Resolution Protocol (ARP) and the Routing Information Protocol (RIP). Gateway Address A Gateway Address is the IP address through which a particular network, or host on a network, may be reached.
Zyxel Pla Series Configuration For Mac
If one network host wishes to communicate with another network host, and that host is not located on the same network, then a gateway must be used. In many cases, the Gateway Address will be that of a router on the same network, which will in turn pass traffic on to other networks or hosts, such as Internet hosts. The value of the Gateway Address setting must be correct, or your system will not be able to reach any hosts beyond those on the same network. Nameserver Address Nameserver Addresses represent the IP addresses of Domain Name Service (DNS) systems, which resolve network hostnames into IP addresses.
There are three levels of Nameserver Addresses, which may be specified in order of precedence: The Primary Nameserver, the Secondary Nameserver, and the Tertiary Nameserver. In order for your system to be able to resolve network hostnames into their corresponding IP addresses, you must specify valid Nameserver Addresses which you are authorized to use in your system's TCP/IP configuration. In many cases these addresses can and will be provided by your network service provider, but many free and publicly accessible nameservers are available for use, such as the Level3 (Verizon) servers with IP addresses from 4.2.2.1 to 4.2.2.6. IP routing is a means of specifying and discovering paths in a TCP/IP network along which network data may be sent. Routing uses a set of routing tables to direct the forwarding of network data packets from their source to the destination, often via many intermediary network nodes known as routers. There are two primary forms of IP routing: Static Routing and Dynamic Routing.
Static routing involves manually adding IP routes to the system's routing table, and this is usually done by manipulating the routing table with the route command. Static routing enjoys many advantages over dynamic routing, such as simplicity of implementation on smaller networks, predictability (the routing table is always computed in advance, and thus the route is precisely the same each time it is used), and low overhead on other routers and network links due to the lack of a dynamic routing protocol. However, static routing does present some disadvantages as well. For example, static routing is limited to small networks and does not scale well. Static routing also fails completely to adapt to network outages and failures along the route due to the fixed nature of the route.
Dynamic routing depends on large networks with multiple possible IP routes from a source to a destination and makes use of special routing protocols, such as the Router Information Protocol (RIP), which handle the automatic adjustments in routing tables that make dynamic routing possible. Dynamic routing has several advantages over static routing, such as superior scalability and the ability to adapt to failures and outages along network routes. Additionally, there is less manual configuration of the routing tables, since routers learn from one another about their existence and available routes. This trait also eliminates the possibility of introducing mistakes in the routing tables via human error. Dynamic routing is not perfect, however, and presents disadvantages such as heightened complexity and additional network overhead from router communications, which does not immediately benefit the end users, but still consumes network bandwidth. TCP is a connection-based protocol, offering error correction and guaranteed delivery of data via what is known as flow control.
Flow control determines when the flow of a data stream needs to be stopped, and previously sent data packets should to be re-sent due to problems such as collisions, for example, thus ensuring complete and accurate delivery of the data. TCP is typically used in the exchange of important information such as database transactions. The User Datagram Protocol (UDP), on the other hand, is a connectionless protocol which seldom deals with the transmission of important data because it lacks flow control or any other method to ensure reliable delivery of the data.
UDP is commonly used in such applications as audio and video streaming, where it is considerably faster than TCP due to the lack of error correction and flow control, and where the loss of a few packets is not generally catastrophic. The Internet Control Messaging Protocol (ICMP) is an extension to the Internet Protocol (IP) as defined in the Request For Comments (RFC) #792 and supports network packets containing control, error, and informational messages. ICMP is used by such network applications as the ping utility, which can determine the availability of a network host or device. Examples of some error messages returned by ICMP which are useful to both network hosts and devices such as routers, include Destination Unreachable and Time Exceeded.
Daemons are special system applications which typically execute continuously in the background and await requests for the functions they provide from other applications. Video editing software free for mac. Many daemons are network-centric; that is, a large number of daemons executing in the background on an Ubuntu system may provide network-related functionality. Some examples of such network daemons include the Hyper Text Transport Protocol Daemon (httpd), which provides web server functionality; the Secure SHell Daemon (sshd), which provides secure remote login shell and file transfer capabilities; and the Internet Message Access Protocol Daemon (imapd), which provides E-Mail services.
Outbound rules Here you can configure permit or deny Access Control List (ACL) statements to determine what traffic is allowed between VLANs or out from the LAN to the Internet. These ACL statements can be based on protocol, source IP address and port, and destination IP address and port. These rules do not apply to VPN traffic. To configure firewall rules that affect traffic between VPN peers, please refer to. Click Add a rule to add a new outbound firewall rule.
The Policy field determines whether the ACL statement permits or blocks traffic that matches the criteria specified in the statement. The Protocol field allows you to specify TCP traffic, UDP traffic, ICMP traffic, or Any. The Sources and Destinations fields support IPs or CIDR subnets. Multiple IPs or subnets can be entered comma-separated. The Src Port and Dst Port fields support port numbers or port ranges. Multiple ports can be entered comma-separated. Port ranges cannot be entered comma-separated.
You can enter additional information in the Comments field. Under Actions you can move your configured rules up or down in the list. You can also click the X next to a rule to remove it from the list. If L3 firewall rules are configured using FQDNs and the MXs firmware version is downgraded to MX 13.3 or earlier, all pieces of the firewall configuration with FQDNs will be removed. Firmware versions below 13.4 do not support FQDNs in L3 firewall rules. FQDN-based L3 firewall rules are implemented based on snooping DNS traffic. When a client device attempts to access a web resource, the MX will track the DNS requests and response to learn the IP of the web resource returned to the client device.
There are several important considerations for utilizing and testing this configuration:. The MX must see the client's DNS request and the server's response in order to learn the proper IP mapping. The communication between the client and DNS server cannot be intra-VLAN (this DNS traffic is not snooped). In some cases, a client device may already have IP information about the web resource it is attempting to access. This could be due to the client having cached a previous DNS response, or a local statically configured DNS entry on the device. The MX may not be able to properly block or allow communications to the web resource in these cases if the client devices do not generate a DNS request for the MX to inspect. An example configuration is included below.
Appliance Services. ICMP Ping: Use this setting to allow the MX to reply to inbound ICMP ping requests coming from the specified address(es). Supported values for the remote IP address field include None, Any, or a specific IP range (using CIDR notation). You can also enter multiple IP ranges separated by commas. To add specific IP addresses rather than ranges, use the format X.X.X.X/32. Web (local status & configuration): Use this setting to allow or disable access to the local management page via the WAN IP of the MX.
Supported values for the remote IPs field are the same as for ICMP Ping. SNMP: Use this setting to allow SNMP polling of the appliance from the WAN. Supported values for the remote IPs field are the same as for ICMP Ping. Layer 7 Firewall Rules Using Meraki's unique layer 7 traffic analysis technology, it is possible to create firewall rules to block specific web-based services, websites, or types of websites without having to specify IP addresses or port ranges. This can be particularly useful when applications or websites use more than one IP address, or when their IP addresses or port ranges are subject to change. It is possible to block applications by category (e.g. 'All video & music sites') or for a specific type of application within a category (e.g.
Only iTunes within the 'Video & music' category). The figure below illustrates a set of layer 7 firewall rules that includes both blocking entire categories and blocking specific applications within a category: It is also possible to block traffic based on HTTP hostname, destination port, remote IP range, and destination IP/port combinations. Port forwarding Use this option to forward traffic destined for the WAN IP of the MX on a specific port to any IP address within a local subnet or VLAN. Click Add a port forwarding rule to create a new port forward. You need to provide the following:. Description: A description of the rule. Uplink: Listen on the Public IP of Internet 1, Internet 2, or both.
Protocol: TCP or UDP. Public port: Destination port of the traffic that is arriving on the WAN. LAN IP: Local IP address to which traffic will be forwarded.
Local port: Destination port of the forwarded traffic that will be sent from the MX to the specified host on the LAN. If you simply wish to forward the traffic without translating the port, this should be the same as the Public port. Allowed remote IPs: Remote IP addresses or ranges that are permitted to access the internal resource via this port forwarding rule. 1:1 NAT Use this option to map an IP address on the WAN side of the MX (other than the WAN IP of the MX itself) to a local IP address on your network. Click Add a 1:1 NAT mapping to create a new mapping. You need to provide the following:.
Name: A descriptive name for the rule. Public IP: The IP address that will be used to access the internal resource from the WAN. LAN IP: The IP address of the server or device that hosts the internal resource that you wish to make available on the WAN. Uplink: The physical WAN interface on which the traffic will arrive. Allowed inbound connections: The ports this mapping will provide access on, and the remote IPs that will be allowed access to the resource.
To enable an inbound connection, click Allow more connections and enter the following information:. Protocol: Choose from TCP, UDP, ICMP ping, or any. Ports: Enter the port or port range that will be forwarded to the host on the LAN.
You can specify multiple ports or ranges separated by commas. Remote IPs: Enter the range of WAN IP addresses that are allowed to make inbound connections on the specified port or port range.
You can specify multiple WAN IP ranges separated by commas. Under Actions you can move a configured rule up or down in the list. Click the X to remove it entirely.
Yahoo Mail Configuration For Mac
1:Many NAT 1:Many NAT, also known as Port Address Translation (PAT), is more flexible that 1:1 NAT. It allows you to specify one public IP that has multiple forwarding rules for different ports and LAN IPs. To add a 1:Many NAT listener IP, click Add 1:Many IP. Public IP: The IP address that will be used to access the internal resource from the WAN. Uplink: The physical WAN interface on which the traffic will arrive. A 1:Many NAT entry will be created with one associated forwarding rule. To add additional rules, click Add a port forwarding rule under the existing rule or rules for a particular 1:Many entry.
Description: A description of the rule. Protocol: TCP or UDP. Public port: Destination port of the traffic that is arriving on the WAN. LAN IP: Local IP address to which traffic will be forwarded. Local port: Destination port of the forwarded traffic that will be sent from the MX to the specified host on the LAN. If you simply wish to forward the traffic without translating the port, this should be the same as the Public port.
Allowed remote IPs: Remote IP addresses or ranges that are permitted to access the internal resource via this port forwarding rule. Bonjour Forwarding Use this feature to allow Bonjour to work between VLANs. Click Add a Bonjour forwarding rule to create a new forwarding rule. Description: Specify a name for the rule. Service VLANs: Select one or more VLANs where network services are running.
Bonjour requests from the Client VLANs will be forwarded to these VLANs. Client VLANs: Select one or more VLANs from which client Bonjour requests can originate. Requests on these VLANs will be forwarded to the Service VLANs. The list of services that can be forwarded include:. All services. AirPlay. Printers.
AFP (Apple file sharing). Scanners. iChat.
Most Viewed Articles
- Scan2cad V8 Keygen For Mac
- Hhh : Steam For Mac
- Mpeg2 Works Advanced 5.0 For Mac
- Moi3d Modeler For Mac
- Charismac Updates Emulex Fc Driver For Mac
- Asset Basset For Mac
- Ati 7500 Drivers For Mac
- Cake Mania 3 Game For Mac
- Parallels Desktop 11.1.1 For Mac
- Trafficcamnz In The New Update For Mac
- Milestone Dlk Keygen For Mac
- Download Minecraft Forge 1.8 For Mac